Understanding Phishing Emails/Finding a Phishing Email

Understanding Phishing Emails, Phishing emails seek to steal important information from a user by pretending to be a bank, financial services provider, email provider, or cloud service, provider.
Occasionally, it gets challenging to recognize phishing emails. These emails, however, frequently have identical patterns and strategies, making them clear and simple to recognize.
Read More: Email Scheduling with Gmail/In Gmail, how to Schedule Email
Understanding Phishing Emails, Indicators of a Phishing Email.
The majority of phishing emails ask for consumers’ login passwords and payment information, such as credit card information. Some also utilize threats and rewards to instill a feeling of urgency in the consumers’ minds or even employ attachments to spread harmful software.
Read More: 6 Ways Secure Your Crypto Investments From Scams
Understanding Phishing Emails, Employing Standard Greetings.
If you receive an email with a generic salutation like “Dear Account Holder” or “Dear Customer,” it can be a phishing scam. Con artists frequently use these salutations to sound more legitimate.
A genuine business or one that you are a customer of would likely address you by name if they were sending you correspondence.
You should use caution and refrain from providing personal information when responding to emails with generic welcomes unless you are confident that the contact is sincere.
Understanding Phishing Emails, Mistakes in Spelling.
Misspellings and bad language that permeate the entire email is one of the telltale indications of phishing emails. Email from a reputable or professional source would be error-free or contain a few minor grammatical and linguistic mistakes.
Suspicious Connections.
It is not advised to open an Email attachment without first verifying the sender. Any emails with attachments that include scripts or encrypted data are advised to be ignored. A good rule of thumb is to avoid opening attachments unless you are certain that the sender is trustworthy.
The scam emails frequently include attachments with the.exe or.zip file extensions. These kinds of hidden files are not detectable by the system or antivirus software. Such attachments may contain malicious software that may be exploited to steal your data if you download or open them.

Important Requests.
Some phishing emails contain a message telling the recipient to act immediately in order to avoid penalties and fines or to receive presents and reward points.
Threats, including the account being closed if no action is made right away, are occasionally included in the phishing emails sent to the recipient. These emails cause recipients to become anxious by instilling a false sense of urgency to respond quickly using a countdown clock or a deadline.
Understanding Phishing Emails, Hidden Links.
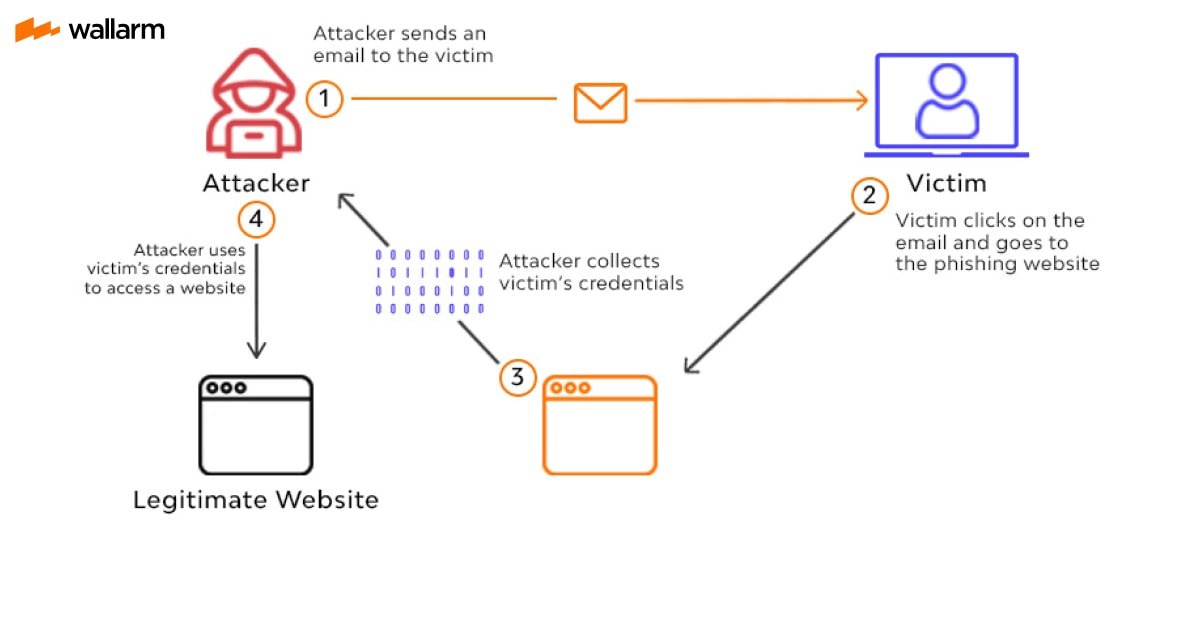
The phishing emails may also contain the URLs of fake websites that pose as legitimate ones. If you click the link, input your login information, or use your payment information on such phone websites, the security of your sensitive data will be jeopardized.
Hover the mouse pointer over the link to find out if it is secure, then look at the lower left corner of the browser window. It is a masked link that could send you to a hazardous website if the URL displayed there does not match the link in the email.
Additionally, make sure the link begins with HTTPS. Avoid clicking on such a link if the URL starts with HTTP or if the browser reports that “your connection is not secure error.” Don’t give any information to these websites if you click on one of these links.
Requests for Payment Information and Login Credentials.
These emails have the appearance of coming from a payment site, such as PayPal, social media, or your bank. They ask for your pin, password, credit card number, and other highly sensitive personal information.
Understanding Phishing Emails, Public email domain usage.
Phishers typically use public email domains like Gmail, Yahoo, and others to send victims phishing emails. Recognize it as a fraud if you get an email purporting to be from a payment service provider, financial institution, or other company but actually coming from a public email address.
When communicating with their clientele, legitimate businesses always utilize their personal email addresses. The domain name of the business that sent the email will very certainly appear in a private email. such as johndoe@paypal.com.

How to Avoid Falling for Phishing Email Scams.
Users must maintain constant vigilance and refrain from taking unwarranted risks with their online security and privacy. Even cautious people are susceptible to phishing scams. Here are some precautions you may take to avoid becoming a phishing scam victim.
- Watch out for emails that ask for personal information from you, such as login passwords and payment card information. A trustworthy business will never email you for your personal information.
- You shouldn’t open any links or attachments that come from unknown sources. These might contain malware and viruses that can steal your data.
- For all of your internet accounts, use solid and distinctive passwords. Password managers can help you establish strong passwords and maintain them on your behalf. Use two-factor authentication as well to provide the accounts an additional layer of security.
- Utilize a reliable antivirus programmer and keep it updated. The majority of antivirus programmers have anti-phishing tools that help users recognize and block phishing emails and websites.
- Use only websites that adhere to the HTTPS protocol. By looking at the address bar of your computer browser, you can identify websites that use this protocol.
- When using your login information to subscribe to any website, use the plus symbol “+” and your email address. Say your email address is my email@gmail.com, for illustration. Instead of using your primary email address when signing up for The Economic Times’ newsletter, enter my email+economictimes@gmail.com.











